关联漏洞
描述
A proof of concept for ReadyAPI 2.5.0/2.6.0 Remote Code Execution Vulnerability.
介绍
# CVE-2018-20580
A proof of concept for ReadyAPI 2.5.0/2.6.0 Remote Code Execution with interactions.
## Intro
In December 2018 I found a new vulnerability in the ([ReadyAPI](https://smartbear.com/product/ready-api/overview/)). It allows an attacker to execute a remote code on the local machine putting in danger the ReadyAPI users including developers, pentesters, etc...
The ReadyAPI allows users to open a SOAP project and import WSDL files that help the users to communicate with the remote server easily.
The WSDL file owner can determine default values of some parameters. An attacker can impersonate a legitimate web service and inject a malicious code into a default value of one of the parameters and spread it to ReadyAPI clients.
When a ReadyAPI client load a malicious WSDL file to his project and send a request containing the malicious code the ReadyAPI will execute the malicious code on the victim's computer.
## PoC
The attack scenario:
+ An attacker impersonates a regular web service with a [WSDL](https://github.com/gscamelo/CVE-2018-20580/blob/master/example.wsdl) containing the malicious code.
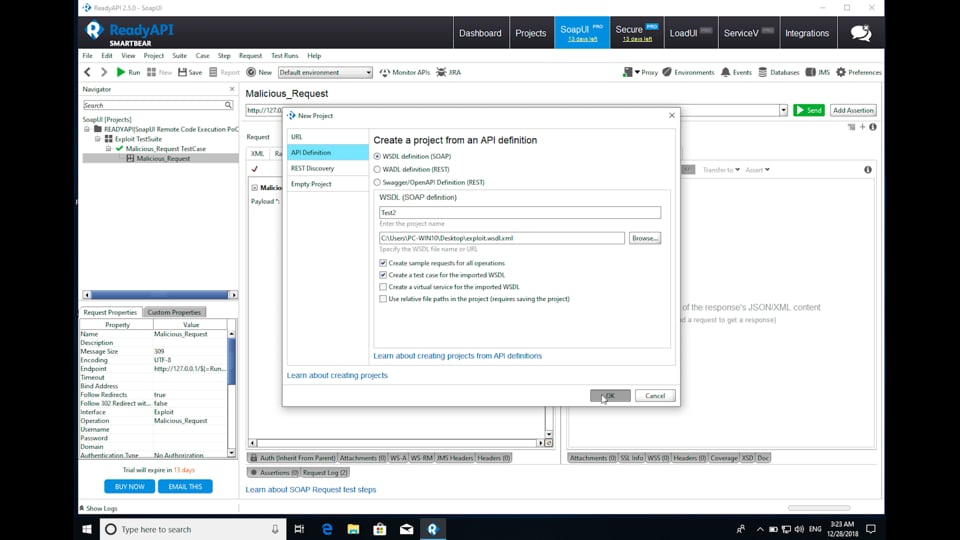
+ The victim creates a new project in the ReadyAPI and loads the malicious [WSDL File](https://github.com/gscamelo/CVE-2018-20580/blob/master/example.wsdl).
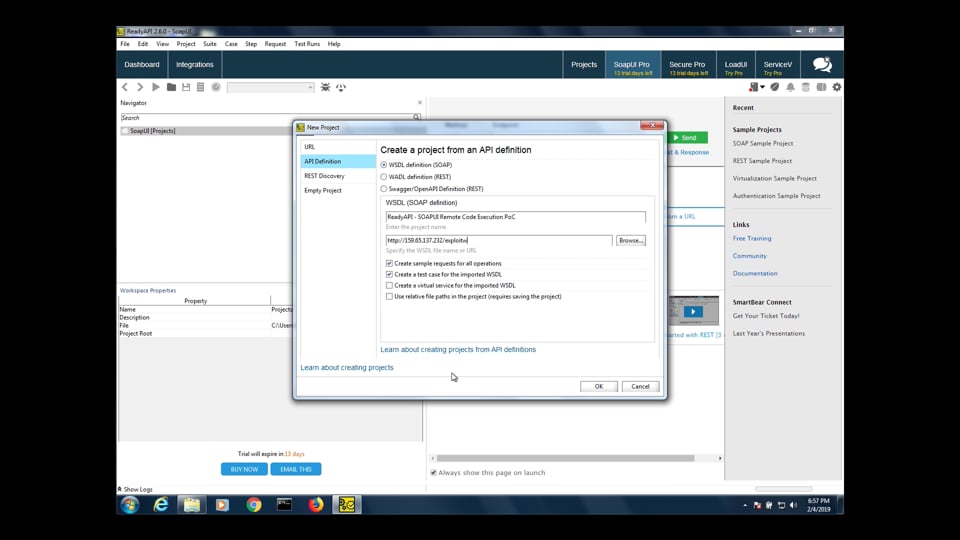
+ The victim decides to send a request to the remote server and the ReadyAPI execute the malicious code.
+ The attacker succeeds in executing malicious code in the victim's machine and take it over.
## Video
ReadyAPI 2.5.0
[](https://vimeo.com/332912402)
ReadyAPI 2.6.0
[](https://vimeo.com/332912473)
## Timeline
+ December 26, 2018 - Vulnerability identified
+ December 28, 2018 - Vulnerability reported
+ February 04, 2019 - Vulnerability reported
+ March 21, 2019 - Bug not fixed
+ May 03, 2019 - Public disclosure
## LINKS
https://www.exploit-db.com/exploits/46796
https://nvd.nist.gov/vuln/detail/CVE-2018-20580
文件快照
[4.0K] /data/pocs/1644fe2afc01f2499585e197d72a0b9a7e227875
├── [2.3K] example.wsdl
└── [2.1K] README.md
0 directories, 2 files
备注
1. 建议优先通过来源进行访问。
2. 如果因为来源失效或无法访问,请发送邮箱到 f.jinxu#gmail.com 索取本地快照(把 # 换成 @)。
3. 神龙已为您对POC代码进行快照,为了长期维护,请考虑为本地POC付费,感谢您的支持。