关联漏洞
标题:
SeaCMS 安全漏洞
(CVE-2024-54879)
描述:SeaCMS是海洋CMS(SeaCMS)公司的一套使用PHP编写的免费、开源的网站内容管理系统。该系统主要被设计用来管理视频点播资源。 SeaCMS 13.1版本存在安全漏洞,该漏洞源于容易受到错误访问控制的攻击,导致攻击者可以利用逻辑漏洞允许任何用户无限期地为会员充值。
描述
CVE-2024-54879
介绍
# 一、Project overview
| **item** | **content** | **remark** |
| ---------------------------- | ------------------------------------------------- | ------------------- |
| Authorized penetration range | http://192.168.88.141/ | Local test |
| Source code download | https://www.seacms.net/SeaCMS_V13.1_install_f.zip | Open source project |
| Scope of vulnerability | SeaCMS_V13.1 | |
# 二、Vulnerability description
## 1、Logic bug - Unlimited top-up members
| **category** | **content** | **remark** |
| ----------------------------- | ------------------------------------------------------------ | ---------- |
| Vulnerability location(URL) | http://192.168.200.141/member.php?action=hyz&gid=3&mon=1 | |
| Vulnerability type | Logic hole | |
| Vulnerability description | SeaCMS has a logical flaw that could be exploited by an attacker to allow any user to recharge members indefinitely | |
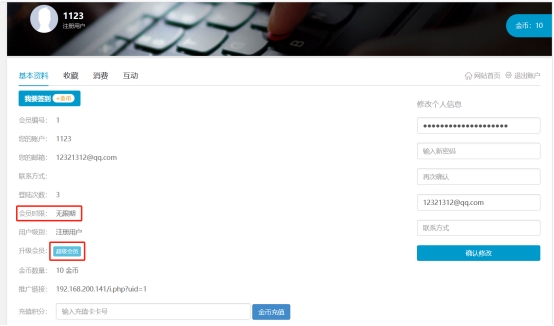
***\*Visit a center and click on Super Member\****
***\*Click on 100 gold per month and grab the pack\****

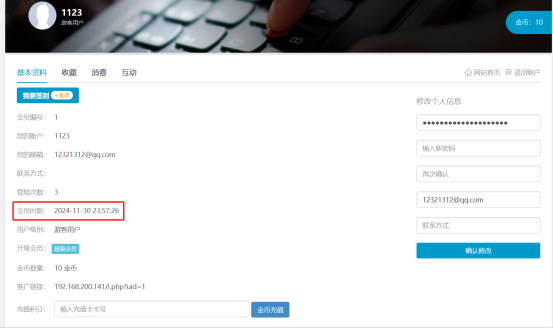
***\*If the gid parameter is changed to 1, the system returns that the recharge is successful\****

***\*Refresh the Personal Center page, successfully add one month membership time\****
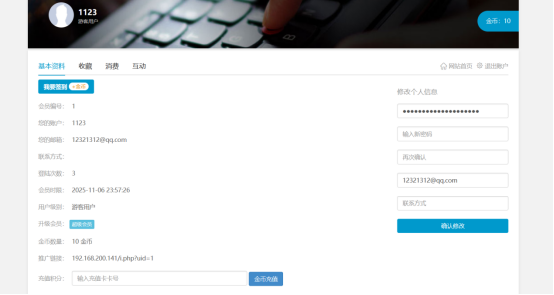
***\*Multiple packages, refresh the personal center page again, you can see the time lengthened\****
文件快照
[4.0K] /data/pocs/7f81dd1a7d12fa9a379410e5f716899a04c73acb
└── [2.1K] README.md
0 directories, 1 file
备注
1. 建议优先通过来源进行访问。
2. 如果因为来源失效或无法访问,请发送邮箱到 f.jinxu#gmail.com 索取本地快照(把 # 换成 @)。
3. 神龙已为您对POC代码进行快照,为了长期维护,请考虑为本地POC付费,感谢您的支持。